74 Interview: Cybersecurity Expert Levin on the Harms of Student Data Hacks
Doug Levin, who chronicles school district computer hacks, discusses the massive Illuminate Education breach and how students can protect themselves

Get stories like this delivered straight to your inbox. Sign up for The 74 Newsletter
Everyone knows rules one and two of Fight Club: You do not talk about Fight Club.
Now it appears that district technology leaders have applied that logic to computer hacks. That’s according to Doug Levin, the national director of The K12 Security Information Exchange, who has spent years chronicling computer hacks on school districts and education technology vendors. Data breaches are a significant and growing threat to schools, he said, yet many district IT officials are hesitant to discuss them.
“Quietly they might confess that this is an issue they lose a lot of sleep over, but they never talk about it publicly, often for fear of looking bad,” said Levin, whose nonprofit group provides threat intelligence to school districts to protect them from emerging cybersecurity risks.
Now, an increasing number of school districts have been forced to notify students and parents that they’ve been duped. In March, New York City Public Schools, the country’s largest district, disclosed that the personal records of more than 820,000 students had been exposed online. The data breach, the largest such incident against a single school district in U.S. history, has since reached far beyond the five boroughs. Other school districts across five states — California, Colorado, Connecticut, Oklahoma and New York — have since acknowledged being victims.
At the center of the debacle is Illuminate Education, a California-based education technology company that helps more than 5,200 school districts track student attendance and grades, among other metrics. Students’ personal information, some of it sensitive, was exposed when hackers breached Illuminate’s servers in January. Exposed information includes students’ names, birth dates, class schedules, behavioral records and whether they qualify for special education or free or reduced-price lunches.

Yet months later, many key details — including the number of districts affected — remain unknown. The company did not respond to requests for comment from The 74.
In New York, state education officials launched an investigation into Illuminate, which city officials accused of misrepresenting its security safeguards.
To gain a better understanding of the hack, The 74 caught up with Levin to discuss how the high-profile data breach occurred, why many critical pieces of information remain elusive and strategies that parents and students can use to protect themselves online.
The interview, which has been edited for length and clarity, was conducted prior to the latest development on the school cybersecurity beat: Chicago Public Schools announced Friday that the personal information of more than half a million students and staff was compromised in a ransomware attack on education technology vendor Battelle for Kids. The data breach was carried out on December 1 and Battelle notified Chicago officials about the attack about a month ago, on April 26.
The 74: The Illuminate Education data breach is the largest known hack of K-12 student records in history?
Doug Levin: The Illuminate Education security incident — we actually don’t know much about what happened — was the single-largest data breach incident affecting a single school district. We still have to see what the numbers bear out for Illuminate Education, and it could still grow significantly in size.
But a couple of years ago Pearson Education experienced a breach of their AIMSweb product. They never disclosed the total number of districts that were affected, but they said that 13,000 of their customers were affected. In fact, the Securities and Exchange Commission fined Pearson for lying to their investors about the scope of the incident. A number of years ago, the education company Edmodo also endured a massive breach.
So there are some large incidents that have happened but the more we learn about the Illuminate Education breach, the worse it does appear to be.
What sets this hack apart from previous incidents?
Some education vendors don’t know a whole lot about the students they’re serving. They may have a student ID, they may know their grades or academic performance in one subject, but not a lot else about that student or their context. The Illuminate Education breach did involve a pretty large swath of sensitive information about students that could be used by criminals to commit identity theft and credit fraud against students.
So that sets it apart.
Unfortunately, it’s the latest and the most high-profile student data breach that is occurring not directly by school districts but by their vendors and partners. A lot of times the security conversation has been focused on the practices of schools themselves and attacks that have targeted schools. There have been a number of high-profile ransomware attacks that have brought school districts to a halt, including in Baltimore County, Maryland, and Albuquerque, New Mexico. Those are very eye-opening incidents and they draw a lot of attention, but they are localized in their impact. They are very significant for those communities, but they only affect those communities.
When a vendor experiences an incident, the impact and the scope of that breach can be massive. If you think about the vendors and suppliers that school districts work with, whether they’re for-profit, nonprofit, or even the state education agencies themselves, if they experience an incident, the scope and magnitude of that incident is likely to be significantly larger.
There’s sort of this idiosyncratic issue in K-12 education where we have been laser focused on issues of student data privacy and a majority of states have now passed new student data privacy regulations in the last five to 10 years largely because the federal law, the Family Educational Rights and Privacy Act, has not been updated since 1974.
But if we only look at this issue through the lens of student data privacy, it is like we have horse blinders on, we are not seeing the full picture. And while ensuring student data privacy is critically important, these are not security laws and they do not adequately address the various ways that unauthorized users can gain access to student data.
In fact, vendors and partners are the most frequent cause of school district data breaches.
This is an era where we need to broaden our lens from student data privacy exclusively to also include security. School districts themselves need to do more due diligence with respect to vendors’ security practices and in making sure they have contractual requirements in place that require the prompt notification and remediation of issues.
With Illuminate Education, it has taken several months for individuals who were affected to find that out. The gap between when the company first learned about the incident and when parents are informed of the incident so they can take steps to protect their children is really too long. We really need to work on tightening that timeframe to protect students from the risks that we are introducing to them.
We don’t know a lot about the scope of the Illuminate Education data breach. How would you describe the company’s overall response? Why does so much remain unclear?
Frankly, it comes down to the state of policy and regulations. In the vast majority of cases, when an incident is experienced by an organization, whether it be by a school district or a partner, one of the first things they will do is look to see what they’re obligated to report under the law.
So setting aside the ethical or moral desire and need to help individuals take steps to protect themselves when you have been at fault in causing an incident, many will look to what they are strictly required to do. And the fact of the matter is that there are many, many loopholes in existing notification laws.
Organizations do not want to share bad news with their customers and stakeholders, and so there are reasons that people don’t like to disclose these things. But there’s also a compelling number of reasons why stakeholders deserve and need to know.
If hacks are not publicly disclosed, policymakers won’t understand the scope of the issue and they can’t take steps to provide more resources to protect against these sorts of threats. That’s exactly the sort of issue we’ve had in K-12. For years, no one talked about the incidents that schools were experiencing, so people thought that schools really weren’t experiencing incidents. That was simply not the case.
Secondly, threat actors that attack schools and their vendors repeat their tactics in predictable ways. If they’re successful at attacking one school district, they will use those exact same tools and techniques against other school districts. So it’s important that organizations share with them a heads-up so that they can take the steps to protect themselves from being compromised in the same ways.
With hacks, there is the potential for people to experience real harms. They can have their identity stolen, tax fraud, credit fraud, they could be embarrassed. They could have things disclosed about them — whether it’s their health status, their legal status, their immigration status — that were never supposed to be public and that may lead to very serious repercussions.
There really is a moral obligation for people to disclose these incidents.
You’ve observed a recent uptick in ransomware attacks. How do districts generally respond to these incidents?
How school districts respond really depends on how proactive they have been in defending against cybersecurity risks. In the best cases, school districts have segmented their networks and made it difficult for that ransomware to spread throughout the district. In those cases, school districts are often able to restore their systems from backups, avoid paying extortion demands, investigate how the ransomware got into their system and plug those holes.
In recent years, ransomware actors have also exfiltrated large amounts of student and staff data before they encrypt and lock those school district computers and demand a ransom. And I should note those ransom demands have been increasing dramatically for K-12 schools. In 2015 or 2016, you might have seen a ransomware demand of $5,000 to $10,000, payable in a cryptocurrency, of course. Today, it wouldn’t be surprising to see a ransomware demand of a million dollars or more being made to a school district.
When school districts are in that place, they’re really between a rock and a hard place at that point. If ransomware spreads across their system, those are the sorts of incidents that close schools for days and kids are sent home.
In those cases, they rely on experts to come in and assess how to rebuild their systems., how to evict ransomware actors from their networks, how to handle the fact that ransomware actors have exfiltrated data already, and to reduce instances where schools have to pay those extortion demands.
Law enforcement will never encourage a victim to pay that extortion demand. Every time a school district does so, they are really just encouraging future threat actors to target school districts with the same sort of techniques.
Even school districts that don’t pay extortion demand face remediation and recovery costs. In Baltimore County, the recovery and remediation costs have been estimated in the millions of dollars, so you’re paying for the cost of ransomware incidents whether you pay that extortion demand or not.
School districts are not exactly flush with cash. Why are schools a good target for hackers? Why are they particularly vulnerable?
I have often heard schools be very surprised when they’re attacked. They’re morally outraged because they’re an institution that is just trying to help kids and they’re being targeted by these criminals.
But you made the statement that schools don’t have a lot of money and I actually want to push back on that. School districts actually manage quite a bit of money every year. They maintain facilities, transportation and food services. They may be the largest employer in many communities.
It is correct, of course, that school districts don’t have enough money to do all the things they would like to do and need to do for kids. I’m not arguing that they are sufficiently funded. But it is not unusual for a school district of medium or large size to have an annual budget in the hundred of millions, and some of the largest districts in the country have annual budgets in the billions. That’s plenty of money to attract the attention of threat actors.
Other than money, school districts and other government agencies have been disproportionately attacked largely because they tend to run IT systems that are older and they also tend to be under-resourced with respect to cybersecurity. They just don’t have the money and the capacity to hire experts in the way that we would hope and certainly not in the way that some private sector organizations do.
And given that public sector organizations like school districts provide essential services and people get very upset if they’re disrupted, they may be susceptible to extortion tactics like ransomware. They also hold a lot of valuable information about those stakeholders that can be repurposed for criminal purposes. It really is a perfect storm here of school districts being, unfortunately, low-hanging fruit for criminals at a time where, as a policy issue, cybersecurity really has not been a priority.
I think this is changing. There are conversations underway in both state legislatures and in Congress looking to provide more resources to school districts for cybersecurity. But this is a marathon not a sprint and, you know, that help has not yet arrived.
What needs to happen legislatively in regards to school district hacks?
There is a need for mandatory reporting. It is very difficult for anyone to get a handle on this issue and how to help schools protect themselves if we don’t know the scope of the issues that schools are facing.
We certainly can’t bring those parties who are responsible to bear unless we get details about those sorts of incidents.
Secondly, there is no floor, there is no minimum cybersecurity risk management practice in a school district. Parents, employees and taxpayers have reasonable assumptions about how school districts protect themselves from ransomware, data breaches and targeted phishing attacks. Yet I think they may be surprised that their expectations are not being met. Setting a minimum cybersecurity expectation on school districts is a common sense step that we can take, and those protections should also be extended to vendors.
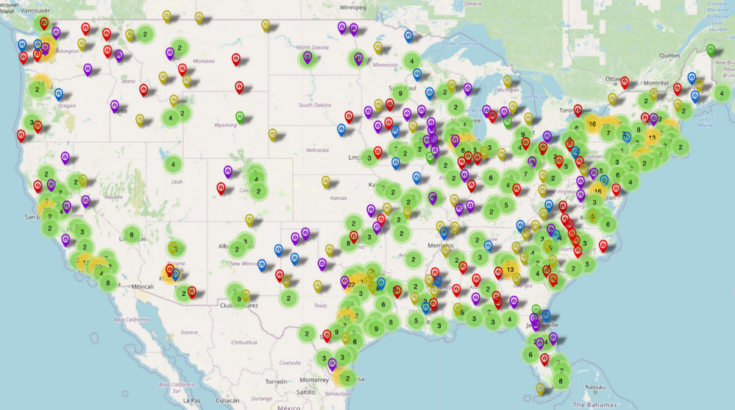
You built a map to track every K-12 data breach since 2016. What key trends and takeaways have you observed?
The majority of those incidents involve student data but a significant minority involve school employee data, including teachers.
A variety of actors are responsible for these incidents. About a quarter are carried out by online criminals targeting school districts, but many are actually the result of the actions of insiders to the schools themselves. Like any large organization, employees make mistakes. School districts may email sensitive data to the wrong people, and very occasionally, school districts have disgruntled employees who do things on their way out the door.
The last group of insiders are the students themselves. An IT leader joked with me once that every school district serving middle and high school students is getting free penetration testing whether they like it or not. The fact of the matter is that a proportion of students are very tech savvy and they do get bored. Kids being kids, they turn their attention to school districts themselves and, in fact, there have been some very large and significant data breaches because students themselves have compromised school district IT systems.
What do students typically do when they compromise school technology?
It depends on the incident. In some cases, they’re seeking to change their grades or their attendance records in a very similar vein to the Ferris Bueller movie. Some kids have even been enterprising and charged their fellow students for the privilege of changing their grades.
But in other cases, they’re simply curious or are interested in making some kind of a statement and are interested in defacing a school website, a school social media account, blasting out emails that they think are funny.
We don’t have any evidence that kids are monetizing their attacks on school districts on the dark web in the way that online criminals do. But having said that, there are a number of cases where students have crossed the line and have gotten entangled with law enforcement because the attacks they’ve carried out against school districts have been so disruptive.
What do we know about the online criminals who target school districts? Who are they, in what cases have they been caught and in what cases have they faced any repercussions?
Cybersecurity attacks have a unique characteristic to them because they can be carried out by individuals anywhere in the world at any time. By and large, the online criminals that are targeting school districts are based overseas and they are based in countries that make it difficult for U.S. law enforcement to reach. As a result, many of these actors are not brought to justice.
A minority of these incidents occur from within the country and in those cases the ability of law enforcement, the FBI in particular, in bringing judgments against those folks is actually pretty good. There was a Texas school district a couple of years ago that was scammed out of several million dollars by a sophisticated phishing attack. It turned out that it was carried out by an individual in Florida who was caught and prosecuted. That person bought Rolexes and sports cars with the money that he stole from that district. But I suspect he is sitting in a jail right now or certainly awaiting the sentencing for that crime.
What lessons does the Illuminate Education breach hold for school districts and education technology vendors?
The story is still being told here, but this is going to be a very cautionary tale both for school districts and for vendors. This is going to evolve depending on the outcome of the investigations in New York. The state of New York has a fairly strict student data privacy regulation and it appears that Illuminate Education was in violation of the rules despite assurances that they were in compliance. So the state of New York has an opportunity to set an example here. Many ed tech companies will be watching very closely.
We’re watching very closely as well. What may happen to renewals from school districts that use products from Illuminate Education? How many customers might they lose?
It would be wise for vendors and suppliers to understand that it is only a matter of time before new regulations require more cybersecurity protections on the data that they hold about school children and school employees.
From a school district perspective, it just underscores the importance of due diligence when they are selecting vendors and the need to consider the security practices of their vendors. This is not a one-time evaluation. Threats and vulnerabilities evolve so we need a continuous evaluation process.
What lessons does this hack hold for parents and students, and what should they do to protect their information online?
It should highlight for parents and students that there are risks in sharing information with schools and their partners. That risk can be managed, but I think it is beholden on parents to ask good questions of their school district about their cybersecurity risk management practices. These don’t have to be very technical questions, but I do think they deserve assurances from the school board and the superintendent that this is an issue that they’re taking seriously and a school district should be able to explain the steps that they’re taking and how they are continuously managing these risks.
If you’re worried about being a potential victim — and I think it is always worth worrying about being a potential victim — there’s a couple of steps that I would encourage both parents and students to take. I would advise parents to freeze their children’s credit record. This is available for free at all of the major credit reporting agencies and it will prohibit an online criminal from stealing the identity of their children and opening credit accounts in their names.
I would also underscore that good password management practices are always useful. I’m talking about not reusing the same username and password that you use for your school accounts for any of your personal accounts. to the greatest extent possible, you want to separate your school life from your private life and the best way to do that is to use a password manager. There are many free password manager applications that are available as well as a number of good paid options.
Get stories like these delivered straight to your inbox. Sign up for The 74 Newsletter

;)
